3. Refer to the exhibit. Host A sends a data packet to host B. What will be the addressing information of the data packet when it reaches host B? Refer to the exhibit. Host A sends a data packet to host B. What will be the addressing information of the data packet when it reaches host B?
4. Which layer of the OSI model defines logical addressing?
5. Which device connects a local LAN to a geographically separate network?
6. Refer to the exhibit. Router1 receives packets addressed as follows:
Source IP address: 192.168.1.88
Destination IP address: 172.16.0.3
Source MAC address: 00-11-12-7a-41-10
Destination MAC address: 00-11-5c-cc-a9-c0
Source Port: 1464
Destination Port: 23
Assuming that Router1 has not been configured with NAT, what will happen to the packets?
7. Refer to the exhibit. If host 1 was to send an HTTP request to the web server that connects to Router2, what type of Layer 2 frame would be sent between Router1 and the ISP?
8. A company needs to connect an office router to a service provider to access a WAN. What device is needed to connect the router to the ISP if the service provider supplies a T1 line for the connection?
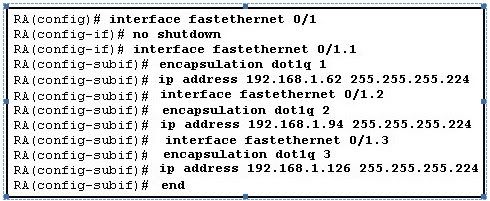
9. Refer to the exhibit. A technician applies the configuration in the exhibit to an unconfigured router. To verify the configuration, the technician issues the show running-config command in the CLI session with the router. What lines should the technician expect to see in the router output from the show running-config command?
10. Refer to the exhibit. If host A sends an IP packet to host B, what will the destination address be in the frame when it leaves host A?
11. Refer to the exhibit. What two facts can be determined from the output of the ping command? (Choose two.)
12. Refer to the exhibit. The switches are in their default configuration. Host A needs to communicate with host D, but host A does not have the MAC address for its default gateway. Which network hosts will receive the ARP request sent by host A?
13. Refer to the exhibit. Which password will the administrator need to use on this device to enter privileged EXEC mode?
14. Refer to the exhibit. Switch1 has only the following commands added to a default Cisco 2960 configuration:
enable secret cisco
line vty 0 4
password Kn0ckkn-cK
login
interface vlan 1
ip address 10.0.1.8 255.255.255.0
no shutdown
Assume that routing between networks is functioning properly and that Switch2 has been properly configured for remote access. What would the result be if the telnet 10.0.2.2 command is issued from Switch1 privileged mode?
15. What caused the following error message to appear?
01:11:12: %PM-4-ERR_DISABLE: psecure-violation error detected on Fa0/8, putting Fa0/8 in err-disable state
01:11:12: %PORT_SECURITY-2-PSECURE_VIOLATION: Security violation occurred, caused by MAC address 0011.a0d4.12a0 on port FastEthernet0/8.
01:11:13: %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/8, changed state to down
01:11:14: %LINK-3-UPDOWN: Interface FastEthernet0/8, changed state to down
16. When configuring a switch to use SSH for virtual terminal connections, what is the purpose of the crypto key generate rsa command?
17. Which three statements are true about full-duplex operation on an Ethernet network? (Choose three.)
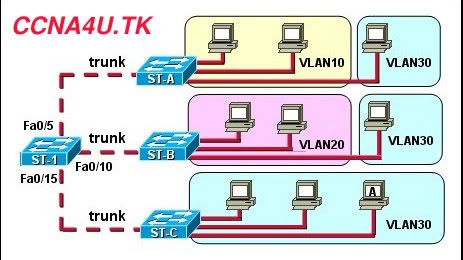
18. Refer to the exhibit. If all the switches have a default configuration, how many broadcast domains are in the network?
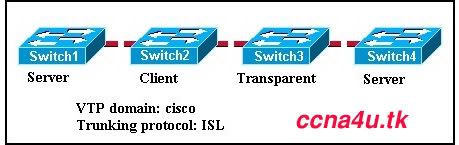
19.
20. Refer to the exhibit. The devices have been configured with static IP addresses as shown. All hosts can communicate with each other but none of the hosts can communicate with the server. What is the cause of this problem?
21. A network host has the IP address 10.250.206.55/20. How many more network devices can be added to this same subnetwork?
22. Which type of Network Address Translation allows a host on a public network consistent access to a specified private inside host?
23. Refer to the exhibit. Which two addresses are "inside global" addresses? (Choose two.)
24. Which addresses are valid host IP addresses given the subnet mask 255.255.255.248? (Choose three.)
25. The router receives a packet with the destination address of 172.16.30.79/22. To which subnetwork does this packet belong?
26. Refer to the exhibit. What is the broadcast address for the subnetwork on which host A resides?
27.
28. What can a network administrator modify on a router to specify the location from which the Cisco IOS loads? (Choose two.)
29. Which two items are required for initial configuration of Cisco routers if the IOS command-line interface is used? (Choose two.)
30. Refer to the exhibit. The router named "myhome" has received a frame from the host 192.168.254.7. The contents of this frame are being sent to host 172.16.14.243. What is the Layer 2 destination address of the frame as it leaves the myhome router?
31. Refer to the exhibit. What two facts can be determined about the network from the exhibited output? (Choose two.)
32. Which set of commands is used to name a router and save the configuration?
33. Which command is used to create an encrypted password that restricts access to the privileged EXEC mode of a Cisco router?
34. Refer to the exhibit. A network administrator working at HostA has problems accessing the FTP server. Layer 3 connectivity testing was successful from HostA to the S0/0/1 interface of RouterB. Which set of commands will allow the network administrator to telnet to RouterB to check its status?
35. What is the purpose of using SSH to connect to a router?
36. Which two statements describe the command ip route 192.168.7.24 255.255.255.248 192.168.7.9? (Choose two.)
37. Which protocol is described as an enhanced distance vector routing protocol?
38. Refer to the exhibit. A network administrator can successfully ping, using IP addresses, between router Jax and router Atlanta. However, when the command telnet Atlanta is entered from the Jax router, the Telnet connection fails. Which two reasons could be the cause of the failure? (Choose two.)
39. From what two locations can a router load the Cisco IOS during the boot process? (Choose two.)
40. Which two statements describe the functions or characteristics of ROM in a router? (Choose two.)
41. Which two statements correctly identify the function of router memory components? (Choose two.)
42. Which router component holds the routing table, ARP cache, and running configuration file?
43. Refer to the exhibit. A network administrator can ping the Denver router, but gets a 'Password Required but None Set' message when trying to connect remotely via Telnet. Which command or sequence of commands must be applied to the Denver router to allow remote access?
44.
45. Which security method uses the Advanced Encryption Standard (AES)?
46. What is the purpose of WEP?
47. A company has an 802.11b wireless access point installed. Which type of wireless NIC is a valid standards-based one but will not work in this environment?
48.
49. A company has a sales team that travels with laptops. On Fridays, the sales members come into assigned cubicles and connect their laptop to the wired network. The company is concerned that unauthorized users could also connect to the network. What can be done to ensure that unauthorized laptops are not connected to the wired network?
50. Refer to the exhibit. For security reasons, information about the HQ R1 router model and IP address should not be accessible from the Site 2 R2 router. What security measure should be implemented?